Zero Trust begins at the edge
Uplift your Cyber Profile
A remarkably powerful, robust, and easy to use solution, delivering Edge Firewall, Router, Secure VPN Access, and Threat Mitigation functionality to homes, businesses, educational institutions, and government agencies.
Firewall Protection
Monitor incoming and outgoing network traffic based on a defined set of security rules.
Secure VPN
Encrypting traffic so no one can see what you do across the Internet from any of your locations
Routing Control
Connect computers and other devices from your business to the world across custom routes priorities.
Threat Mitigation
real-time context correlation monitoring, detection, and alerting of security events and incidents.
Secure Networks, Measurable Outcomes
Enterprise-grade network security built on open architectures
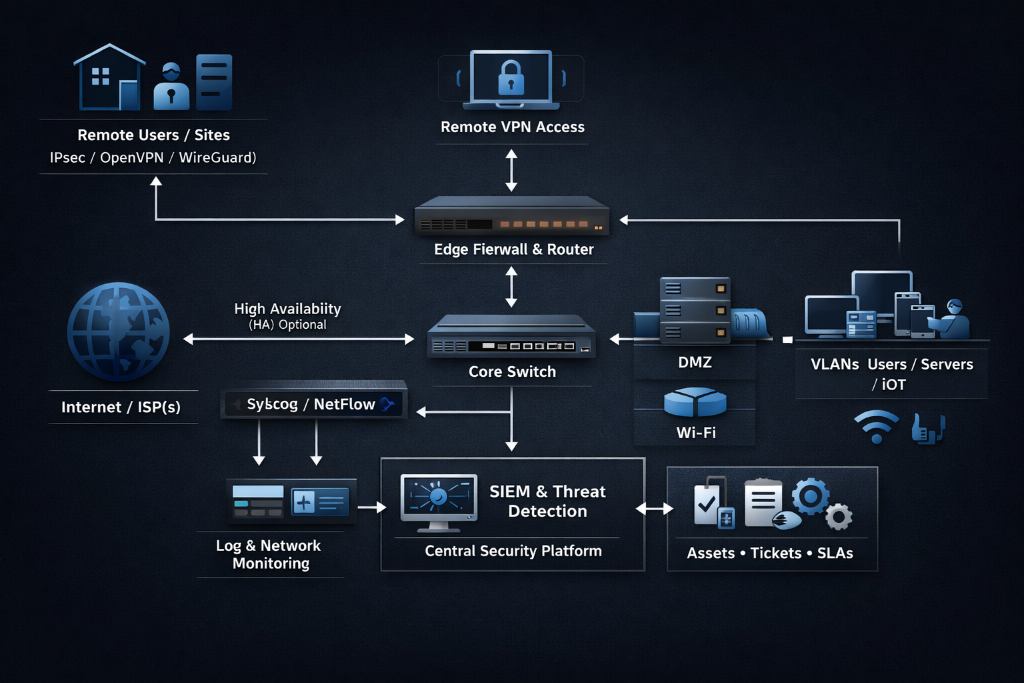
At Globalgen, we deliver end-to-end network security by engineering three layers into a single operating model: pfSense at the edge (firewall/router/VPN), Wazuh in the SOC layer (SIEM +EDR/XDR analytics and response), and Asset Management for IT operations (asset + service management). Each platform is proven in its domain. Our firewall provides a security-focused network perimeter with routing, VPN, and high-availability options. Our SOC unifies SIEM and XDR capabilities; and Asset Management provides asset visibility and ITIL-aligned service management so security operations translate into accountable work.
Closed-Loop Cyber Security
We don’t just “install tools.” We design a closed-loop security system
where edge telemetry, endpoint behavior, and IT workflow stay
synchronized so threats are detected faster, contained earlier, and
documented properly for audit and governance.
| Capability | Key features we implement | Business benefit |
|---|---|---|
| Edge firewall | Stateful filtering, rules per ingress interface, antispoofing/ingress filtering patterns | Reduced attack surface, predictable policy enforcement at the perimeter |
| VPN & secure access | IPsec, OpenVPN, WireGuard options; rules tailored per VPN type | Secure remote work + site-to-site connectivity without “flat network” exposure |
| Routing & resilience | Multi-WAN throughput + reliability; policy routing; load balancing/failover; HA with stateful failover | Higher uptime, resilient internet connectivity, fewer “single point of failure” outages |
| SIEM analytics | Central event aggregation, ruleset-driven alerting, log analysis pipeline | Faster detection + triage with consistent alert definitions and evidence trails |
| Endpoint protection | System inventory (Syscollector), vulnerability detection correlation, active response scripts | Identify vulnerable workloads, reduce dwell time, automated containment for selected events |
| IT asset & service management | Asset inventory (manual + agent-driven), ITIL-aligned ticketing, SLAs/OLAs, REST API | Security becomes managed work: owners, due dates, escalation, audit-ready records |
Business Benefits and Capabilities
Why this stack works as a unified security program
Most environments fail at the handoffs: firewall events don’t reach the SIEM cleanly, endpoint detections aren’t tied to assets, and incident handling turns into email threads without evidence.
Our approach closes these gaps by using a security appliance for deterministic network control, SOC for
centralized detection and response, and asset register to operationalize security into repeatable ITIL workflows and measurable SLAs/OLAs.
End Point Protection
Monitoring, Alerting, and Incident Response Strategy
We treat monitoring as a pipeline: collect → normalize → detect → triage → respond → document.
On the collection side, our security appliance can forward logs to a centralized system for long-term storage and reporting, while our SOC (XDR/SIEM) Layer explicitly supports collecting, analyzing, and storing logs from endpoints, network devices, and applications -including via syslog.
On the detection side, we generate alerts after processing events and can forward those alerts into its storage/indexing components (including default forwarding using Filebeat).
On the response side, our Active Response can execute response scripts (for example, blocking malicious network access or deleting malicious files) when alerts match defined conditions. We implement this conservatively with change control and staged rollout to avoid business disruption.

Extended detection and response
Active XDR protection from modern threats
A comprehensive security platform that detects, analyzes, and responds to threats across multiple IT infrastructure layers. Get analysis real-time correlation and context. Active responses are granular, encompassing on-device remediation so endpoints are kept clean and operational.
Security information and event management
A comprehensive SIEM solution
Security Information and Event Management aggregating and analyzing telemetry data. Providing business with real time threat detection from various sources like endpoints, network devices, cloud workloads, and applications for a broader security coverage.
Packaging, Pricing, and Next Steps
Pricing and packaging options
Pricing is inherently scope-dependent (endpoint count, log volume,
retention, HA requirements, integration depth, compliance needs).
Pricing provided is standard indicative pricing and may vary upon completion of a detailed discovery and scoping process. All amounts are exclusive of GST.
Foundation
$1000 /mo
| Best for | Single site, practical hardening |
| Security scope | Edge firewall policy, VPN, baseline logging |
| SOC scope | Core SIEM alerts + dashboards |
| IT/Asset scope | Asset baseline + ticket workflows |
| Monitoring & response | Business-hours monitoring; incident ticketing |
Professional
$1500 /mo
| Best for | Multi-site, higher assurance |
| Security scope | Multi-WAN resilience, segmentation, HA option |
| SOC scope | SIEM + endpoint inventory + vulnerability detection |
| IT/Asset scope | CMDB enrichment + SLAs/OLAs |
| Monitoring & response | Extended-hours monitoring; tuned detection; playbooks |
Enterprise
$2500 /mo
| Best for | Regulated/critical environments |
| Security scope | HA pair, advanced routing, governance controls |
| SOC scope | Clustered SIEM+ design; automation; active response (approved use-cases) |
| IT/Asset scope | HA-ready CMDB; reporting; audit SLAs/OLAs workflows |
| Monitoring & response | 24/7 monitoring option; IR retainer option |
Deployment Models
Deployment Models
Deployment Models We Deliver
Flexible security architecture designed to match your operational, regulatory, and scalability requirements.
Globalgen designs flexible security architectures to align with regulatory requirements, operational constraints, and scalability objectives. Our solutions can be deployed on-premises, in the cloud, or in hybrid configurations - ensuring resilience, performance, and centralized visibility.
On-Premises
Full Control. Internal Hosting.
Security appliances deployed at each site with internally hosted monitoring and service management - ideal for regulated environments requiring data residency, governance control, and scalable high-availability architecture.
Cloud-Hosted Security Operations
Edge Protection. Central Intelligence.
Security appliances at each location with monitoring, analytics, and service workflows hosted in a secure cloud environment - delivering centralized multi-site visibility, automation, and elastic scalability without expanding on-prem infrastructure.
Hybrid
Local Resilience. Centralized Oversight.
Edge security and local data collection at each site with centralized analytics and service management ensuring operational continuity during WAN disruption while maintaining enterprise-wide monitoring and compliance visibility.
Compliance, Standards Alignment & Scalability
Australian Cyber Security Alignment
Our security architectures align with Australian guidance, including the Essential Eight baseline strategies and ASD gateway security principles. We design perimeter controls with explicitly authorised traffic flows, layered inspection, and strong incident response capability. For APRA-regulated organisations, our approach supports CPS 234 expectations around control effectiveness, threat detection, and incident response planning.
International Standards Mapping
Where required, we align solution design to recognised frameworks such as ISO/IEC 27001 and NIST incident response guidance. Policies, logging, asset management, access controls, and incident response processes are structured to support governance, audit readiness, and continuous improvement. This ensures practical alignment with internationally recognised best practice.
Performance & Scalability
We engineer for resilience and growth. Our security appliances eliminate single points of failure through high-availability design and stateful failover. Monitoring and analytics platforms scale from single-node deployments to clustered architectures, while service management systems can be load-balanced and deployed in high-availability configurations to support mission-critical operations.